Azure Disk Encryption using PowerShell
Azure Disk Encryption (ADE) provides volume encryption for the OS and data disks of Azure virtual machines by using the DM-Crypt feature in Linux or the BitLocker feature of Windows. ADE is integrated with Azure Key Vault to help you control and manage the disk encryption keys and secrets. In this post, I want to show you how to encrypt the system volume of an existing Windows virtual machine using PowerShell.
Important: Before encrypting your Azure virtual disks, check the following link to verify that your virtual machines meet the requirements.
Requirements: This tutorial assumes that you already have an Azure Key Vault. To learn how to create a Key Vault, see this link.
Azure PowerShell Workaround #
If you want to know how to install the PowerShell Azure module on your machine, check out this link.
The simplest way to get started is to sign in interactively at the command line.
Connect-AzAccount
This cmdlet will bring up a dialog box prompting you for your email address and password associated with your Azure account.
If you have more than one subscription associated with your mail account, you can choose the default subscription. To perform this task, we will use the following commands:
Get-AzSubscription
Select-AzSubscription -Subscription "My Subscription"
Set the variables #
Here, we define the characteristics of our environment
$resourceGroupName = "RG-DEMO-NE"
$location = "northeurope"
$vmName = "VM-DEMO-NE-001"
$keyVaultName = "KV-DEMO-NE"
Azure Key Vault Access Policy #
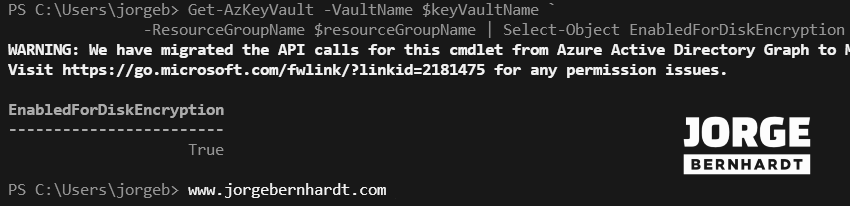
As I mentioned before, ADE requires an Azure Key Vault to control and manage disk encryption keys and secrets. Your Key Vault must have the option for disk encryption enabled. To find out if your Key vault already meets this requirement, you should run the following command.
Get-AzKeyVault `
-VaultName $keyVaultName `
-ResourceGroupName $resourceGroupName `
| Select-Object EnabledForDiskEncryption
To enable disk encryption for an existing Key Vault, you should use the Set-AzKeyVaultAccessPolicy cmdlet with the following syntax.
Set-AzKeyVaultAccessPolicy `
-VaultName $keyVaultName `
-ResourceGroupName $resourceGroupName `
-EnabledForDiskEncryption
Enable the disk encryption #
The Set-AzVmDiskEncryptionExtension cmdlet requires some values from your Key Vault resource. You can save the Key vault object in a variable and pass these values as parameters.
$KeyVault = Get-AzKeyVault `
-VaultName $keyVaultName `
-ResourceGroupName $resourceGroupName
To encrypt your virtual machine, you must use the Set-AzVmDiskEncryptionExtension cmdlet with the following syntax.
Set-AzVMDiskEncryptionExtension `
-ResourceGroupName $resourceGroupName `
-VMName $vmName `
-DiskEncryptionKeyVaultUrl $KeyVault.VaultUri `
-DiskEncryptionKeyVaultId $KeyVault.ResourceId `
-VolumeType "OS"
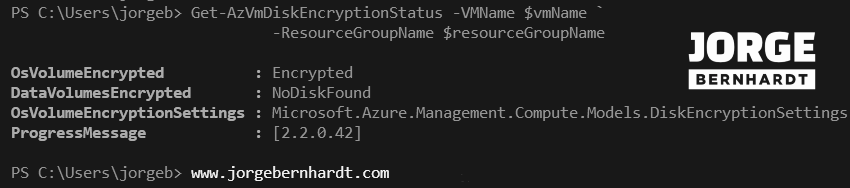
Check the encryption status #
You can check the disk encryption status using the Get-AzVmDiskEncryptionStatus cmdlet with the following syntax.
Get-AzVmDiskEncryptionStatus `
-VMName $vmName `
-ResourceGroupName $resourceGroupName
To get all the encryption secrets used to encrypt virtual machines in a key vault, you need to use the Get-AzKeyVaultSecret cmdlet with the following syntax.
Get-AzKeyVaultSecret -VaultName $KeyVaultName `
| where { $_.Enabled} `
| format-table @{Label="MachineName"; Expression={$_.Tags['MachineName']}}, @{Label="VolumeLetter"; Expression={$_.Tags['VolumeLetter']}}, @{Label="EncryptionKeyURL"; Expression={$_.Id}}
Disable the disk encryption #
To disable the encryption on your virtual machines, you should use the Disable-AzVMDiskEncryption cmdlet. This cmdlet is not supported on Linux virtual machines.
Disable-AzVMDiskEncryption `
-VMName $vmName `
-ResourceGroupName $resourceGroupName `
-VolumeType "OS"
-VolumeType: This parameter accepts the following values. [ All, OS, and Data]
Remove the Encryption extension #
If you want to remove the disk encryption extension and the associated configuration on your virtual machine, you should use the Remove-AzVMDiskEncryptionExtension cmdlet. This cmdlet will fail if encryption on the virtual machine has not been first disabled.
Remove-AzVMDiskEncryptionExtension `
-VMName $vmName `
-ResourceGroupName $resourceGroupName
Thanks for reading my post. I hope you find it helpful. If you want to know more about Azure Disk Encryption, check out this link.