How to Audit PowerShell Usage Using Transcription
Hello, today I want to show you how to use the group policy to configure the registry transcription to audit the use of PowerShell on servers. Requirements: This tutorial assumes that the target system already has WMF 5.x installed or upgraded. The group policy setting to enable and configure Windows PowerShell logging capabilities can be found in the following GPO folder. Computer Configuration\Policies\Administrative Templates\Windows Components\Windows PowerShell
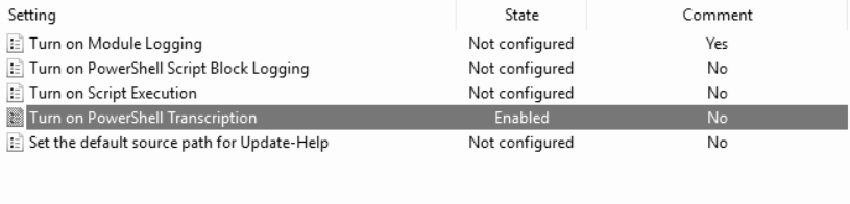
Turn on PowerShell Transcription #
This policy setting allows you to capture the input and output of Windows PowerShell commands in text-based transcripts.
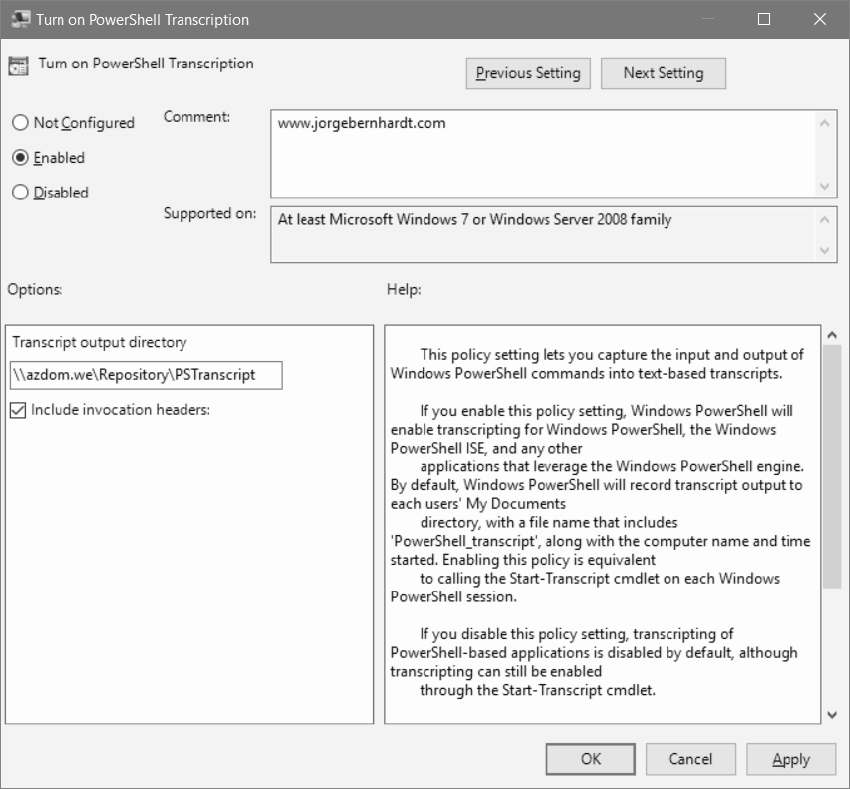
Transcription Output Directory: You can specify an alternative location for the transcript files. The best practice says that you should store it in a shared directory with write-only permissions on a remote server.
Include invocation headers: If you want to have a time stamp for each command that is executed through PowerShell.
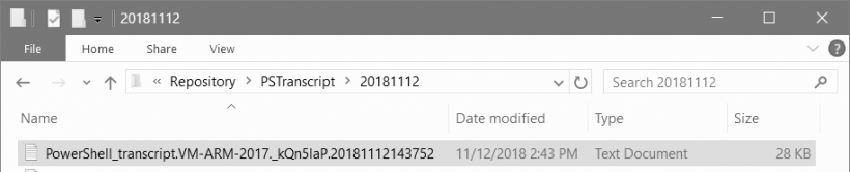
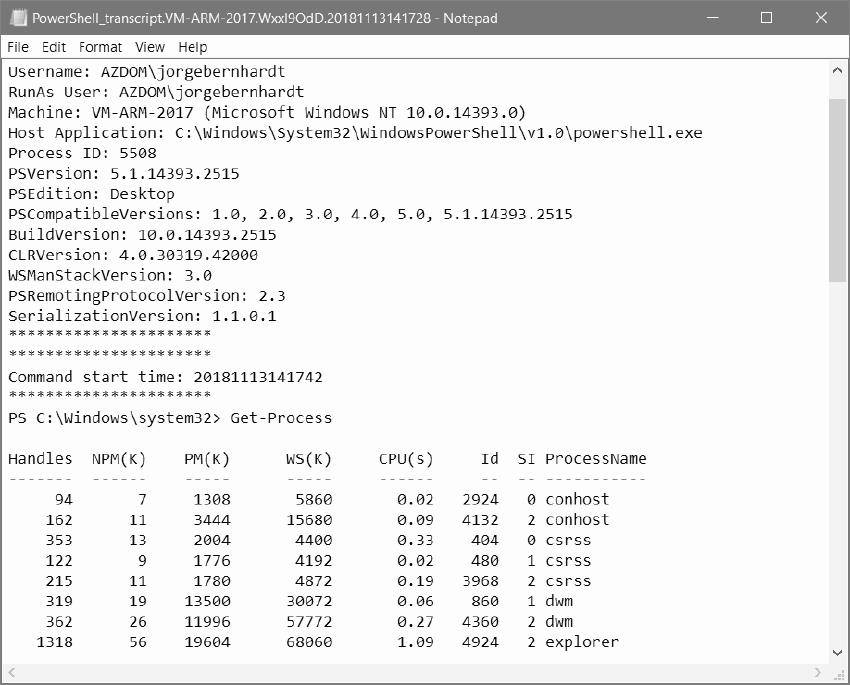
In the following screenshot, you can see the contents of a transcription file.
If you want to know more about Audit PowerShell Usage using Transcription, check out this link.