How to enable SMB encryption on Windows Server
Since Windows Server 2012 and Windows 8, we have version 3.0 of the SMB protocol. This version includes several SMB security enhancements, one of which is encryption. Implementation of this enhancement enables us to encrypt data transferred over the network between the SMB file server and the client. In this post, I want to show you how to enable SMB encryption for the entire file server or only for specific file shares using PowerShell.
Important: If a client that does not support SMB 3.0 tries to access an encrypted shared repository, the event will be logged on the file server with ID: 1003 and the client receives an access denied error message.
PowerShell Workaround #
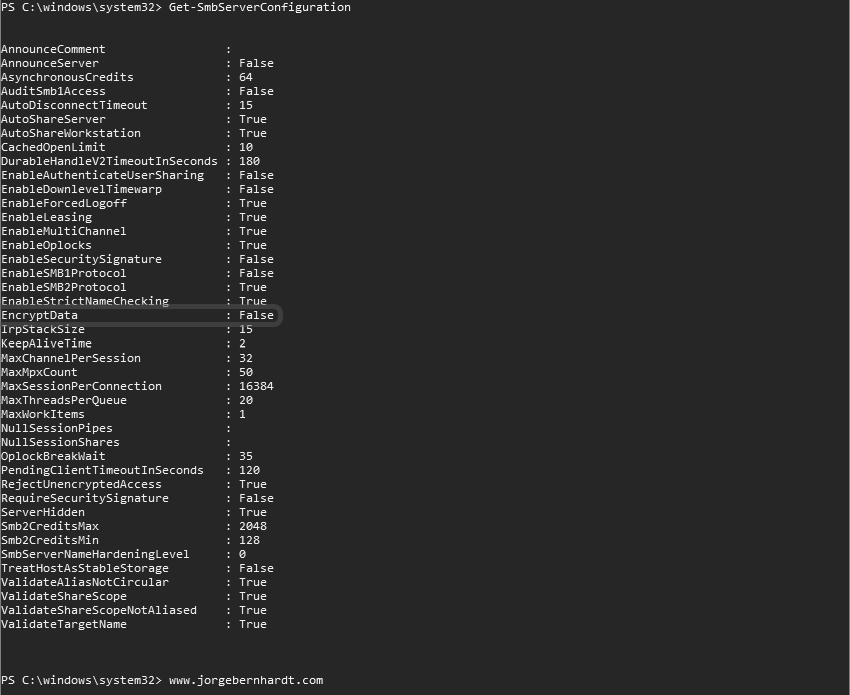
First, we must check the current configuration of the SMB server by executing the following command.
Get-SmbServerConfiguration
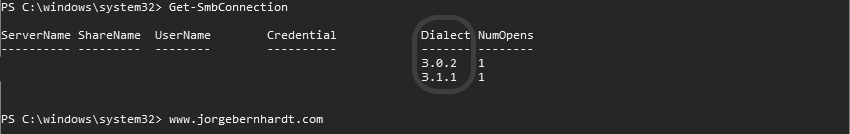
Get-SmbConnection
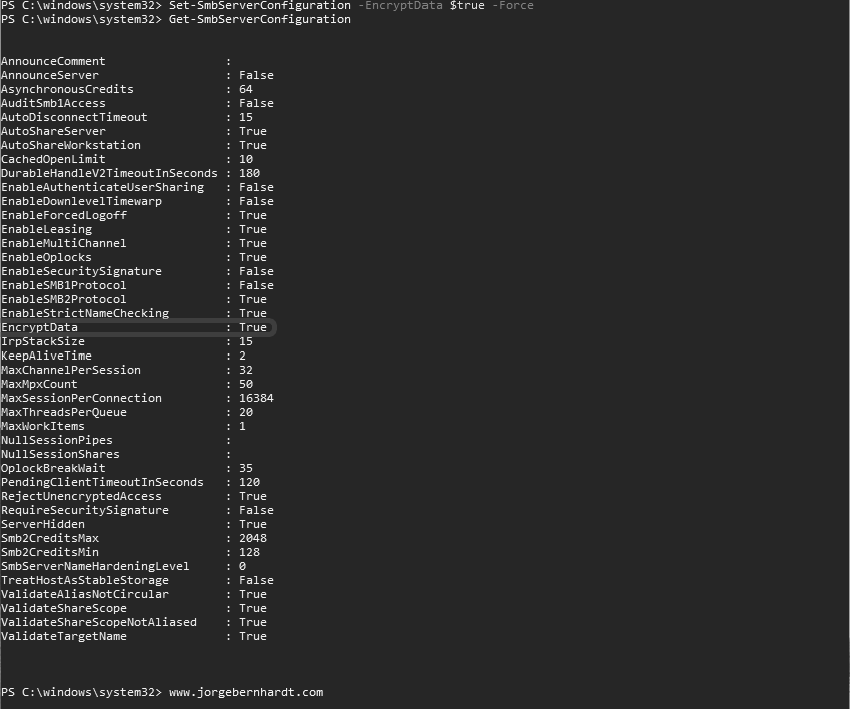
Set-SmbServerConfiguration `
-EncryptData $true
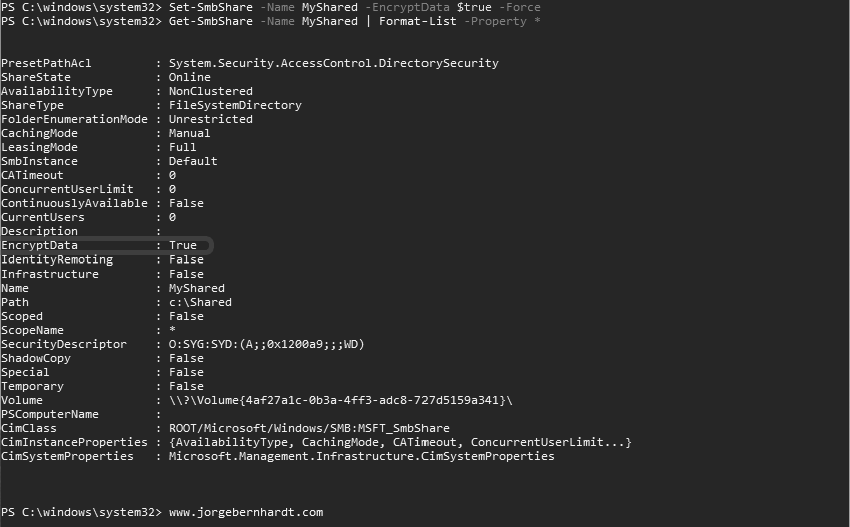
Set-SmbShare `
-Name MyShared `
-EncryptData $true
Get-SmbShare `
-Name MyShared `
| Format-List -Property *
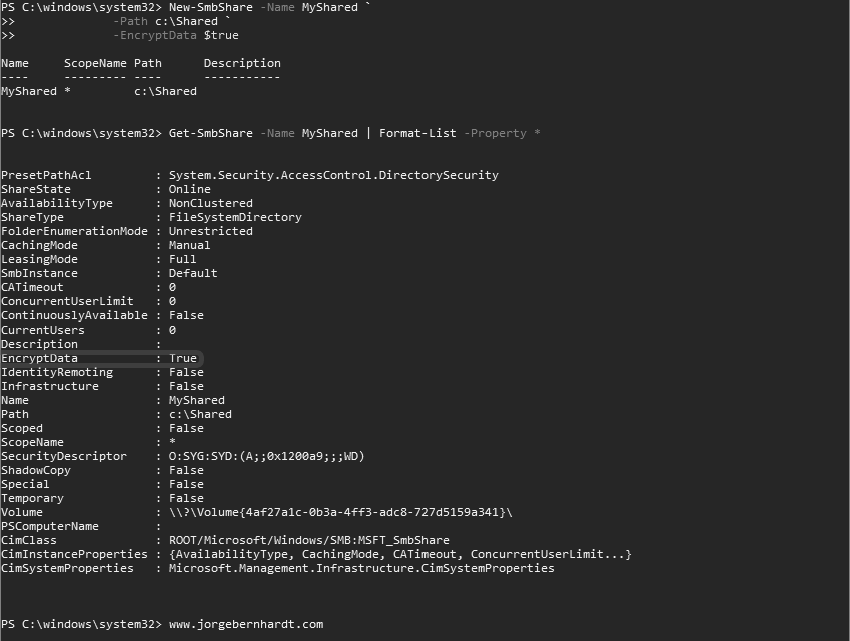
New-SmbShare `
-Name MyShared `
-Path c:\Shared `
-EncryptData $true
Get-SmbShare `
-Name MyShared `
| Format-List -Property *
Set-SmbServerConfiguration `
-RejectUnencryptedAccess $true
However, in some circumstances, you may need to allow unencrypted access to clients that do not support SMB 3.0. To do this, use the following command.
Set-SmbServerConfiguration `
-RejectUnencryptedAccess $false
Thanks for reading my post. I hope you find it useful.
If you want to know more about SMB security enhancements, check out this link.